In 2021 Cyber Monday, we will implement our Incident Responder module, where security analysts can add the necessary technical and practical knowledge to guide the steps towards becoming an incident responder, and where incident responders can improve themselves and sharpen their skills on current threats.
We understand better that there is no 100% security by reading the news that institutions that invest heavily in cyber security are hacked every day. Instead of hoping that a cyber security incident will not happen, it should be considered what to do when a incident occurs. As a result of the interviews and surveys we conducted with SOC team leaders and managers, we observed that institutions mostly complain about the lack of sufficient technical level analysts.
We are happy to share with you our new Incident Responder module, which we have developed to overcome these problems and take the analysis skills to a higher level.
If you can relate with even one of the items below, our Incident Responder plan is for you!
With the Incident Responder module, you will have access to the investigation cases specially created for users who only have the Incident Responder plan.
Each investigation case is based on real-life incidents encountered by experienced incident responders working at LetsDefend. Moreover, there is a one-to-one simulation of cyber-cases that took place before, in the cases included in LetsDefend.

Users with the Incident Responder plancan access devices with real Windows and Linux operating systems through the browser and perform incident response and analysis.

Moreover, it is as easy as just clicking the "Connect" button, without the need for VPN and downloading any files!

There are also technical articles in which we explain how to respond to an incident, how to analyze a cyber attack, and incident response processes.
Since the technical content we have written addresses both the incident responders who do not know how the incident response should be, and who know how the incident response should be, but have deficiencies, everyone has their own content. Moreover, these contents belong to both Windows and Linux operating systems!

In each of the investigation cases included in the Incident Responder plan, there are Official Write-ups prepared by experienced incident responders. After completing your investigation, you can check the accuracy of the analyzes you have made through Official Write Ups, detect your missing or incorrect analyzes and get a different perspective during the incident response.


There are evaluation questions in the training content that you can evaluate yourself. By connecting to live machines via the browser, you can search for answers to the questions asked and get the necessary points to complete the training. We agree that the traditional question-answer method, where only general knowledge and theoretical information is asked, does not lead the analyst to learn new things. After obtaining theoretical information with the Incident responder package, you can connect to the live machine to solve the questions at the end of the training content and reinforce the explained topic.

But the practice doesn't just end here! After completing the training, do not forget to solve the specially prepared incident response cases, where you can improve your incident response skills.
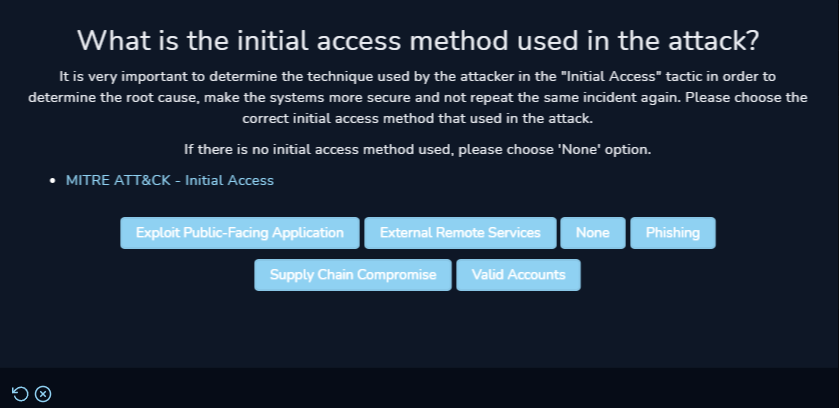
With the playbooks we have specially prepared for Incident Responders, you can learn what to do in what order during the incident response, compare the answers you gave at the end of the playbook with the correct answers and identify your deficiencies.